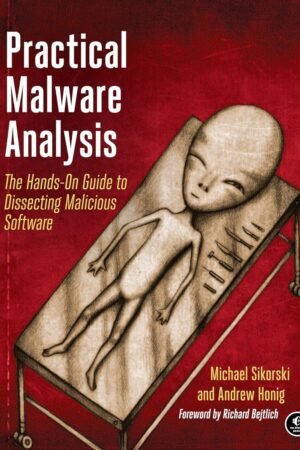
Cyber Operations
Original price was: 950EGP.820EGPCurrent price is: 820EGP.
Know how to set up, defend, and attack computer networks with this revised and expanded second edition.
You will learn to configure your network from the ground up, beginning with developing your own private virtual test environment, then setting up your own DNS server and AD infrastructure. You will continue with more advanced network services, web servers, and database servers and you will end by building your own web applications servers, including WordPress and Joomla!. Systems from 2011 through 2017 are covered, including Windows 7, Windows 8, Windows 10, Windows Server 2012, and Windows Server 2016 as well as a range of Linux distributions, including Ubuntu, CentOS, Mint, and OpenSUSE.
Key defensive techniques are integrated throughout and you will develop situational awareness of your network and build a complete defensive infrastructure, including log servers, network firewalls, web application firewalls, and intrusion detection systems.
Of course, you cannot truly understand how to defend a network if you do not know how to attack it, so you will attack your test systems in a variety of ways. You will learn about Metasploit, browser attacks, privilege escalation, pass-the-hash attacks, malware, man-in-the-middle attacks, database attacks, and web application attacks.
What You’ll Learn
- Construct a testing laboratory to experiment with software and attack techniques
- Build realistic networks that include active directory, file servers, databases, web servers, and web applications such as WordPress and Joomla!
- Manage networks remotely with tools, including PowerShell, WMI, and WinRM
- Use offensive tools such as Metasploit, Mimikatz, Veil, Burp Suite, and John the Ripper
- Exploit networks starting from malware and initial intrusion to privilege escalation through password cracking and persistence mechanisms
- Defend networks by developing operational awareness using auditd and Sysmon to analyze logs, and deploying defensive tools such as the Snort intrusion detection system, IPFire firewalls, and ModSecurity web application firewalls
Who This Book Is For
This study guide is intended for everyone involved in or interested in cybersecurity operations (e.g., cybersecurity professionals, IT professionals, business professionals, and students)
Size: A4(20*28cm)
Printing: 80 gm – color
Cover: Softcover
Shipping:
Delivery within Egypt usually takes 3-5 working days, depending on the workload. In peak times, delivery takes longer.
After purchasing, you can track your order easily from here.
Returns:
We print books specifically for you, and we offer a 30-day replacement guarantee for any printing or packaging issues. If you have any problem, you can contact us at 01055395959
Quality Warranty
What you see is what you get, else you get your money back.
Diverse Collection
We curate a diverse selection to cater to every reading taste.
24/7 Support
Our customer support is ready & excited to help with any issue.
Budget-Friendly
We offer a wide range of books at affordable prices to everyone.
Testimonials
What Our Customers Say