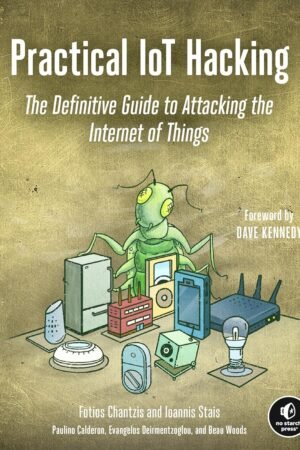
Social Engineering Attack
Original price was: 250EGP.200EGPCurrent price is: 200EGP.
“The social engineering attack is presented in the first chapter of the book. It covers the definition, background, motives, and outcome of the social engineering attack. The life cycle of a social engineering attack is covered in the second chapter of the book. Attack formulation, information collecting, preparation, cultivating relationships, exploitation, and debriefing are the six phrases used by social engineering attackers throughout the life cycle. The basic concepts of social engineering attacks are covered in the third chapter of the book. The six principles of social engineering include scarcity, commitment, authority, social proof, reciprocity, social proof, and social proof. Various forms of social engineering attacks are discussed in the fourth chapter of the book. The physical method, social approach, reverse social engineering approach, technical approach, and socio-technical approach are the five main forms of social engineering attacks. Identity theft is discussed in five of the book’s chapters. The purpose of the information that attackers stole from users is explained in this chapter. Social engineering tools are covered in the book’s six chapters. Organizations deploy a variety of toolkits to informally teach their staff members and identify organizational weaknesses. The seven chapter of the book covers the countermeasures for social engineering attacks. There are three ways to counter the social engineering attack includes policy and procedures, education, and technical. The eighth chapter of the book covers the laws that are related to social engineering attacks. Many governments proposed many laws which directly or indirectly related to social engineering attacks. The future of social engineering attacks is covered in the ninth chapter of the book. Some of the technology that will be utilized in the future for social engineering purposes is covered in this chapter”
Size: A4(20*28cm)
Printing: 80 gm – color
Cover: Softcover
Shipping:
Delivery within Egypt usually takes 3-5 working days, depending on the workload. In peak times, delivery takes longer.
After purchasing, you can track your order easily from here.
Returns:
We print books specifically for you, and we offer a 30-day replacement guarantee for any printing or packaging issues. If you have any problem, you can contact us at 01055395959
Quality Warranty
What you see is what you get, else you get your money back.
Diverse Collection
We curate a diverse selection to cater to every reading taste.
24/7 Support
Our customer support is ready & excited to help with any issue.
Budget-Friendly
We offer a wide range of books at affordable prices to everyone.
Testimonials
What Our Customers Say